Introduction
Most enterprise fraud stacks are built to detect account takeover after it’s already succeeded. Login anomaly rules fire at authentication. Transaction models fire at monetization. By both points, the attacker is already inside.
Knowing how to detect account takeover in real-time means shifting detection upstream – to behavioral signals, device trust, credential exposure feeds, and session integrity monitoring that activate before any fraudulent transaction is attempted.
This guide covers six proven detection methods, the ATO lifecycle stages where each applies, and the architectural gaps that leave most organizations exposed well into the fraud window.
Introduction: The Detection Gap That Costs Enterprises Millions
ATO fraud losses hit $15.6 billion in 2024, according to Javelin Strategy & Research. Yet for most enterprise fraud teams, the architecture meant to stop it fires alerts after the damage is already in motion.
That’s the real problem. Not the signals. The timing.
Most detection stacks activate at login anomalies or transaction review, both of which sit downstream of active compromise. The credential has already been tested, the session is live, and the attacker is inside. What fraud leaders should be measuring is the fraud exposure window: the period between credential compromise and detection. That window is where losses accumulate.
This article is written for fraud operations professionals accountable for that window. You’ll leave with a structured framework for orchestrating detection signals across the full ATO lifecycle, from credential harvesting through to pre-monetization activity, not a list of generic tool recommendations.
To reduce that window, fraud teams first need a clear view of how account takeover fraud progresses across the full attack lifecycle, from credential exposure to account access and monetization.
Why most ATO detection happens too late
Most enterprise detection stacks are wired to catch the wrong moment.
Login anomaly scoring and transaction review are the workhorses of ATO detection, and they’re genuinely useful. But they activate at Stage 3 of a six-stage attack lifecycle, after credentials are already compromised and an attacker has authenticated. By that point, the fraud exposure window is already open.
The math is unforgiving. The longer the gap between credential compromise and detection, the larger the loss surface. SpyCloud’s 2025 Identity Exposure Report confirmed ATO attacks increased 24% year-over-year in 2024. The IBM X-Force 2025 Threat Intelligence Index found identity abuse accounted for 30% of all initial access vectors, making it the single most common entry point. And Proofpoint’s 2024 ATO research found 62% of monitored organizations experienced at least one successful account takeover.
The structural problem isn’t that login monitoring is wrong. It’s that it’s incomplete. Credential harvesting, account testing, and session establishment all occur upstream of the login event, invisible to detection tools that only watch the door after it’s already been opened.
The account takeover lifecycle: where detection actually needs to happen
By the time most alerts fire, the attacker has already moved on.
ATO isn’t a single event. It’s a sequence. Where your detection activates within that sequence determines how much exposure you carry. Here’s how the lifecycle actually unfolds:
- Stage 1 – Credential harvesting
Attackers collect valid credentials through phishing sites, infostealer malware, and breach repositories. No login attempt has occurred yet. The victim has no idea their credentials are already in circulation.
- Stage 2 – Account testing and credential validation
Automated bots probe login endpoints at scale to identify which stolen credentials are still active. Akamai’s 2024 Securing Apps report recorded 26 billion credential stuffing attempts per month, a nearly 50% increase over 18 months. This is industrialized validation.
- Stage 3 – Successful authentication
Valid credentials gain access. This is where most detection stacks activate. It’s also already Stage 3 of a six-stage attack.
- Stage 4 – Session manipulation and privilege change
Post-login, attackers modify account details: email address, phone number, MFA device. These changes lock out the legitimate user and prepare the account for monetization, often before any transaction is flagged.
- Stage 5 – Monetization
Fraudulent transfers, loyalty point redemption, data exfiltration, or account resale. The fraud exposure window has fully opened.
- Stage 6 – Detection and response
Where most organizations currently detect ATO. By this point, the damage is active and the response shifts from prevention to remediation.
The structural problem is clear. Detection at Stage 3 or later means the attacker has already completed credential validation and gained access. Every stage you move detection upstream, toward Stage 1 or 2, compresses the fraud exposure window before it can widen.
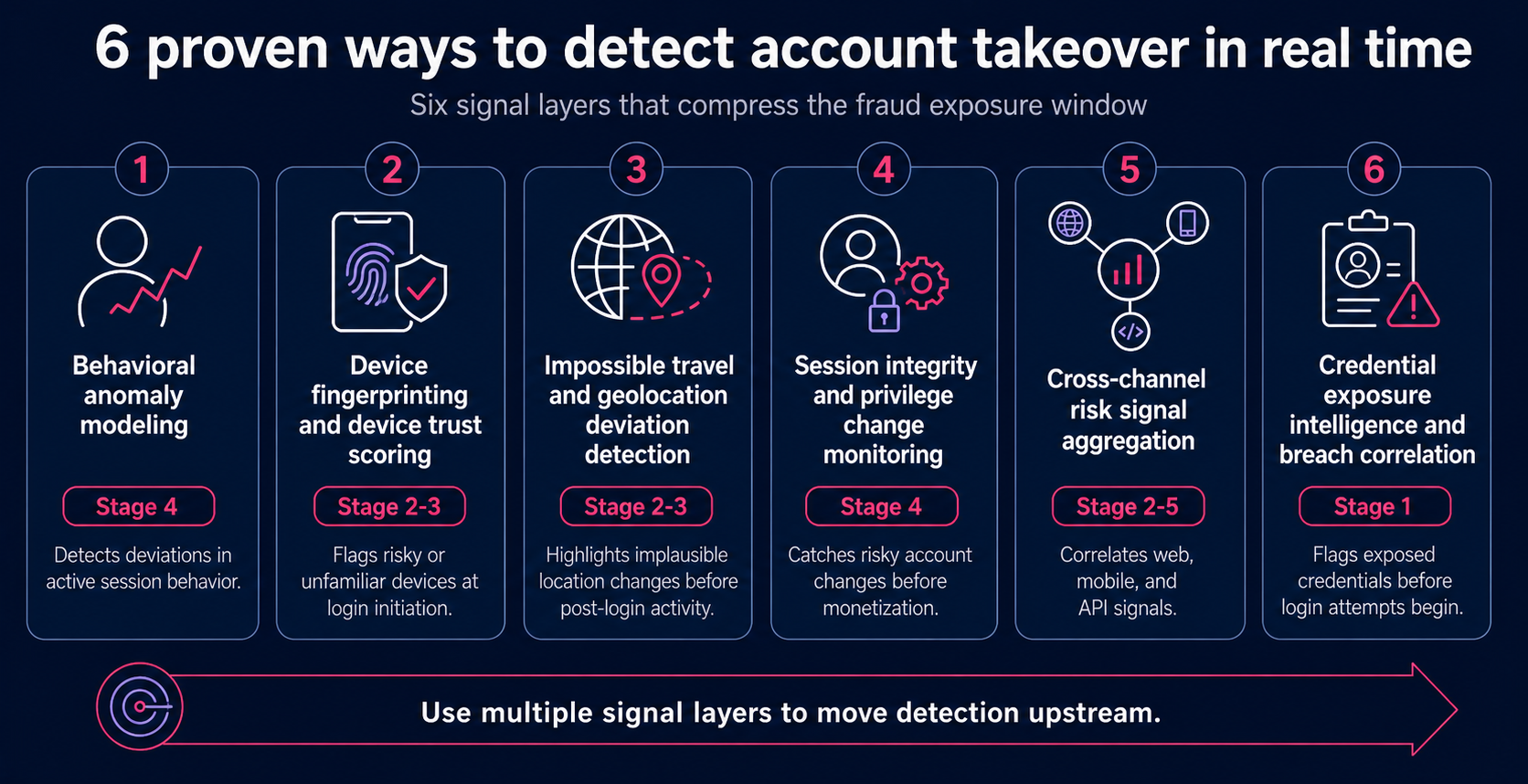
6 proven ways to detect account takeover in real-time
No single signal catches account takeover reliably. Fraudsters are too adaptive, and attack paths vary too widely across channels and account types. Effective real-time ATO detection requires orchestrating multiple signal layers across the full attack lifecycle, from credential testing through to post-login session activity.
The six methods below each address a distinct phase of the ATO chain. The question each one answers is the same: how does this reduce the time between compromise and detection? Used in combination, they compress the fraud exposure window. Used in isolation, they leave gaps.
According to Verizon’s 2025 Data Breach Investigations Report, stolen credentials remain the leading initial access vector in confirmed breaches. Upstream detection across all six layers isn’t a nice-to-have. It’s a structural necessity.
Step 1: Deploy Behavioral Anomaly Modeling Across Full Session Behavior
Behavioral anomaly modeling builds per-user baselines across navigation patterns, transaction velocity, feature usage, session duration, and typing cadence, then flags deviations during active sessions. Unlike static rule-based detection, adaptive ML models surface novel deviations that rules never anticipated.
This shifts detection from Stage 5 (monetization) to Stage 4 (session manipulation), compressing the exposure window before damage occurs.
One practical caveat: these models require sufficient historical data, so they’re less reliable for new accounts or low-frequency users. As OneSpan notes, monitoring behavioral patterns throughout transaction sessions is now a regulatory expectation, not just a best practice.
Step 2: Implement Device Fingerprinting and Device Trust Scoring
Device fingerprinting collects browser attributes, OS version, screen resolution, hardware identifiers, and IP reputation to build a persistent device identity tied to a user’s historical access pattern. Unlike behavioral models that require post-login activity, device trust signals are available at authentication initiation, compressing detection to Stage 2-3.
New devices, emulated environments, VPN masking, and spoofed attributes all elevate session risk scores before a single transaction fires.
Score device trust as a continuous variable, not a binary pass/fail. Sophisticated actors using clean virtual machines or residential proxies can still evade fingerprinting. Treat it as a signal, not a verdict.
Step 3: Apply Impossible Travel and Geolocation Deviation Detection
Impossible travel detection flags sequential access events from locations that are physically implausible within the elapsed time. That’s a clear indicator of credential sharing, session token theft, or proxy-masked access.
Risk scoring combines IP geolocation, time-delta between events, and device fingerprint matching to separate genuine anomalies from VPN noise or corporate proxy routing. Treat it as a signal, not a verdict.
Geolocation data is available at authentication (Stages 2-3), enabling risk elevation before any post-login activity begins.
Step 4: Monitor Session Integrity and Privilege Change Events
Most attackers don’t go straight to the transaction. Between login and monetization, they modify account settings: changing the registered email, updating the phone number, adding a new MFA device, or registering a new beneficiary. The FBI IC3 confirms that in nearly all social engineering ATO cases, attackers change account passwords before initiating transfers.
Monitoring these events in real time, rather than logging them for post-incident review, activates detection at Stage 4.
Velocity rules add further signal: multiple account modifications within a single session indicate active manipulation, compressing the exposure window before any fraudulent transaction fires.
Step 5: Aggregate Risk Signals Across Web, Mobile, and API Channels
Attackers don’t stay in one lane. A credential stuffing campaign might probe your mobile app, then execute account takeover through your web login or API layer, exploiting gaps between siloed detection models.
A low-risk mobile session followed by a high-velocity API call from a different device should elevate composite risk. The EY Loyalty System Fraud Report (2025) notes that credential stuffing campaigns frequently target mobile endpoints lacking web-equivalent bot detection controls.
Cross-channel aggregation surfaces patterns invisible to any single-channel model, cutting detection latency before monetization occurs.
Step 6: Integrate Credential Exposure Intelligence and Breach Correlation
This is the most upstream detection method available, and the one most commonly absent from enterprise stacks.
By monitoring dark web repositories, breach databases, and infostealer logs for credentials tied to your user base, you can flag high-risk accounts before an attacker attempts a single login. When a credential surfaces in a breach feed, the associated account is queued for step-up authentication or proactive outreach immediately.
This moves detection to Stage 1, the maximum possible compression of the fraud exposure window. Signal quality is high: SpyCloud’s 2025 Identity Exposure Report found that 70% of users exposed in breaches reused previously compromised passwords, making breach correlation a reliable ATO risk indicator.
Feed freshness and deduplication directly affect signal accuracy.
Connecting ATO Detection to Upstream Threat Activity: From Impersonation to Credential Harvest
Most detection stacks are wired to the wrong end of the attack chain.
Digital impersonation attacks – phishing sites, cloned login pages, spoofed brand portals – are the primary mechanism through which credentials are harvested at Stage 1 of the ATO lifecycle. Yet most detection architectures activate at Stage 3 or later, after those credentials have already been used. According to the Verizon 2025 Data Breach Investigations Report, stolen credentials were involved in 88% of breaches within the web application attack pattern. The supply chain feeding ATO is hiding in plain sight.
Upstream threat visibility changes the math. If your organization detects a phishing site actively harvesting credentials from your users right now, you don’t wait for a suspicious login to act. You flag at-risk accounts, trigger step-up authentication, or initiate proactive outreach before a single login attempt occurs, compressing the fraud exposure window to near-zero for those accounts.
As David Mattei, Strategic Advisor at Datos Insights, noted: “Awareness of these attacks typically occurs only after damage is done… Memcyco’s technology provides financial institutions with visibility into fraud attempts before credentials are compromised, addressing a persistent blind spot in traditional security frameworks.”
Detection architectures that ignore credential stuffing campaigns and the phishing infrastructure feeding them are structurally blind to the earliest, and most actionable, signal layer available.
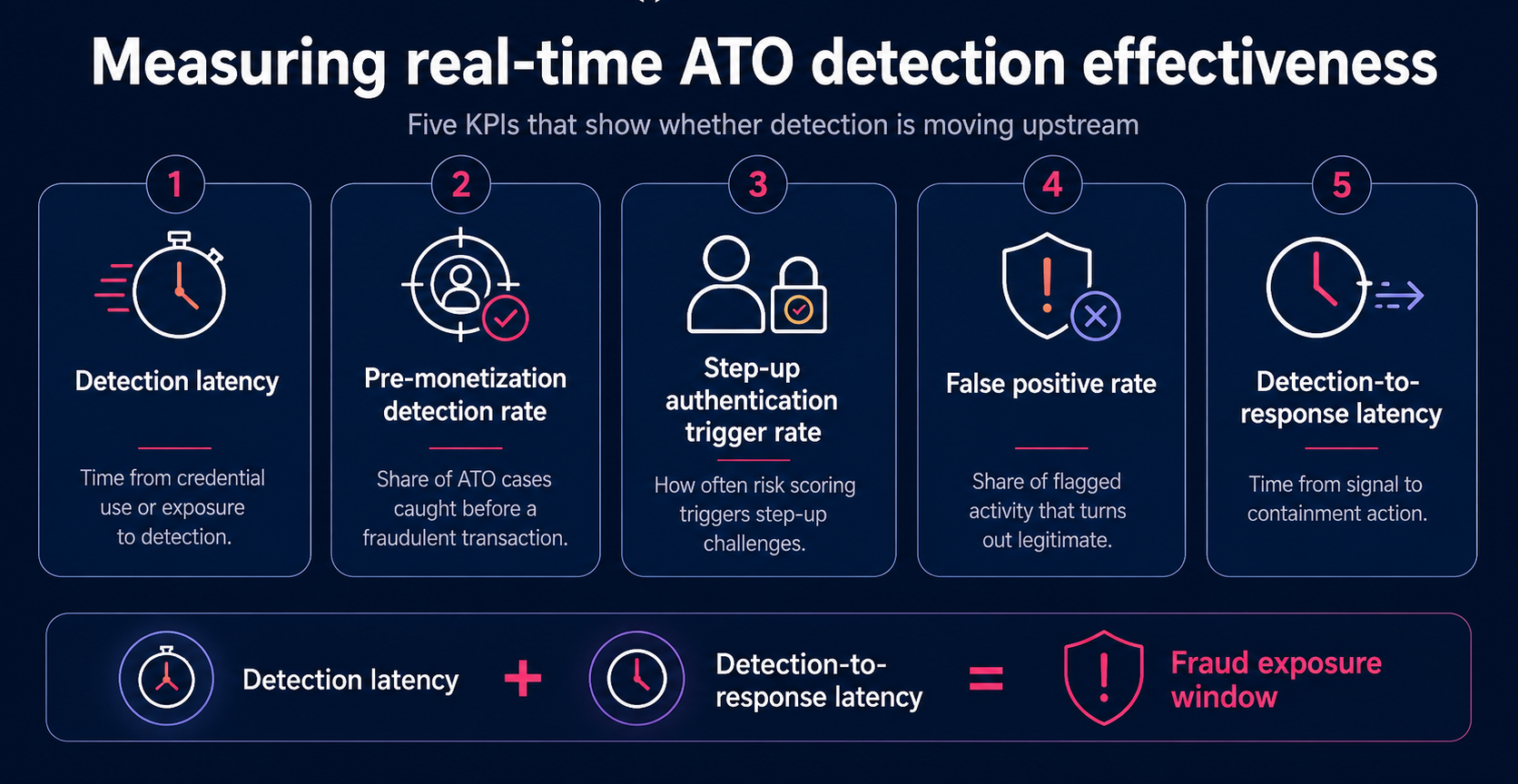
Measuring Real-Time ATO Detection Effectiveness
You can’t compress a detection window you’re not measuring. These five KPIs give fraud leaders a defensible, operationally grounded way to evaluate whether their detection architecture is actually moving the point of detection upstream.
- 1. Detection latency – Time elapsed from credential use, or credential exposure if upstream visibility is in place, to detection signal. Benchmark against your own historical baseline rather than industry averages, which vary significantly by sector and attack sophistication.
- 2. Pre-monetization detection rate – The percentage of confirmed ATO cases detected before a fraudulent transaction was initiated. This is the primary measure of detection-window compression. Rates vary based on attack complexity and architecture maturity. Not all compromise is detectable before monetization.
- 3. Step-up authentication trigger rate – The rate at which risk scoring triggers automated step-up challenges. Monitor for both under-triggering (missed detections) and over-triggering (false positive pressure on legitimate users). It’s a proxy for detection sensitivity, not a verdict on accuracy.
- 4. False positive rate – The percentage of flagged sessions that resolve as legitimate activity. High false positive rates erode customer experience and reduce analyst trust in the detection system over time.
- 5. Detection-to-response latency – Time from detection signal to containment action: session termination, account lock, or step-up trigger. This measures your response architecture’s operational efficiency, not just detection speed. The gap between these two numbers is where fraud exposure lives.
The difference these metrics make is concrete. Customers using Memcyco’s platform report cutting ATO incident handling from 72 hours to under one hour. That’s not a marginal improvement. It’s a structural shift in exposure window.
Common ATO Detection Mistakes and How to Avoid Them
Most detection gaps aren’t caused by missing tools. They’re caused by how existing tools are wired.
- 1. Treating login anomaly detection as the primary ATO signal
Login events sit at Stage 3 of the ATO lifecycle. By the time a login anomaly fires, credential harvesting and account testing have already run their course. Login monitoring is necessary, but it can’t be the anchor signal. Pair it with upstream indicators to move detection earlier.
- 2. Operating siloed channel detection
Separate fraud models for web, mobile, and API don’t just create blind spots, they create exploitable ones. Sophisticated attackers probe channels independently, knowing cross-channel correlation is weak. As Sift’s Q1 2026 Digital Trust Index confirms, fraud has shifted upstream to account-level attacks spanning multiple touchpoints. Unified signal aggregation across channels is the corrective.
- 3. Relying on batch-scored behavioral models
Hourly or daily batch scoring can’t support real-time containment. By the time a batch model flags a session, the intervention window has closed. Continuous scoring pipelines are required for any meaningful detection-to-response latency reduction.
- 4. Ignoring privilege change events as fraud signals
Email address changes, MFA device additions, and recovery option updates are high-fidelity pre-monetization signals. Most stacks log these events but don’t score them in real time. That’s a missed detection opportunity at exactly the right stage.
- 5. Measuring detection effectiveness by transaction fraud rate alone
This metric is blind to pre-monetization ATO. If an attacker modifies account details and exits before transacting, the transaction fraud rate stays clean while exposure is already active. Add pre-monetization detection rate and detection latency to your measurement framework.
Building Your ATO Detection Architecture: A Verification Checklist
Most mature fraud operations have partial coverage across these areas. The goal isn’t a perfect score, it’s identifying where your detection window is widest.
Stage 1-2: Pre-login (credential harvesting and account testing)
- Do you have credential exposure monitoring for your user base?
- Do you have visibility into phishing infrastructure targeting your brand?
- Is credential stuffing activity on your login endpoints monitored in real time?
Stage 3: Authentication
- Is device trust scoring applied at authentication initiation?
- Are geolocation anomalies scored as part of session risk, not just logged?
Stage 4: Post-login, pre-monetization
- Are privilege change events (email, phone, MFA device, beneficiary) scored in real time?
- Is session behavior monitored continuously after authentication, not just at transaction initiation?
Stage 5: Cross-channel coverage
- Are risk signals correlated across web, mobile, and API channels?
- Is API endpoint activity included in your behavioral anomaly models?
Response architecture
- Is step-up authentication triggered automatically by risk score thresholds?
- Is detection-to-response latency measured and tracked as an operational KPI?
Gaps in Stages 1-2 are the most consequential. If your detection stack only activates at Stage 3 or later, credential compromise is already complete before your first signal fires.
Early-Stage Threat Visibility Reduces ATO Exposure – Here’s Where to Start
If your detection architecture activates at transaction review, the fraud window is already open.
For most enterprise fraud teams, the highest-leverage move isn’t refining login anomaly rules. It’s gaining visibility into credential harvesting before compromised credentials ever reach your login endpoints.
See how Memcyco’s Account Takeover solution approaches pre-monetization detection and early-stage threat visibility. If you’re evaluating how upstream signals fit your existing anti-fraud and authentication stack, the Fraud & Risk Teams page shows how the PoSA platform surfaces signals your current tools can’t.
Conclusion
Real-time ATO detection isn’t about faster alerts. It’s about moving detection upstream – to credential harvesting, session anomalies, and pre-monetization signals that fire before damage occurs. The six methods in this guide, combined with cross-channel signal aggregation and breach correlation, give fraud teams the coverage to compress the exposure window significantly.
Reduce Your ATO Exposure Window Before Monetization Occurs
If your detection stack activates at transaction review, fraud exposure may already be active. Explore how upstream threat visibility changes the detection equation – and what early-stage signals your current architecture is missing.
Explore Early-Stage ATO Visibility
FAQs
Q: What is the difference between real-time ATO detection and real-time ATO alerting?
A: Real-time alerting is reactive: a human analyst receives a notification after a detection signal has already fired. Real-time detection architecture is proactive: signals are continuously orchestrated across behavioral, device, geolocation, and credential intelligence layers, and automated responses — step-up authentication, session termination, account flag — are pre-configured to execute without requiring analyst intervention. The distinction matters because detection-to-response latency in alert-driven architectures is bounded by analyst availability, while automated response architectures can contain threats in seconds.
Q: At what stage of the ATO lifecycle do most enterprise detection stacks activate?
A: Most enterprise detection stacks activate at Stage 3 (Successful Authentication) or Stage 5 (Monetization) of the ATO lifecycle. Login anomaly detection fires at Stage 3, while transaction fraud models fire at Stage 5. Both are downstream of credential harvesting (Stage 1) and account testing (Stage 2), meaning the fraud exposure window is already open by the time most detection signals fire. Pre-monetization detection — catching ATO at Stage 4, during session manipulation and privilege changes — requires continuous post-authentication monitoring that many stacks do not implement.
Q: How does credential exposure intelligence reduce ATO detection latency?
A: Credential exposure intelligence monitors dark web repositories, breach databases, and infostealer malware logs for credentials associated with your user base. When a credential appears in a breach feed, the associated account can be flagged for step-up authentication or proactive outreach before the attacker attempts to use it — compressing the detection window to Stage 1 of the ATO lifecycle, before any login attempt occurs. The effectiveness of this approach depends on the freshness and coverage of the intelligence feed, as stale breach data provides limited operational value.
Q: What KPIs should fraud leaders use to measure ATO detection effectiveness?
A: The five most operationally relevant KPIs for ATO detection architecture are: (1) Detection Latency — time from credential use to detection signal; (2) Pre-Monetization Detection Rate — percentage of ATO cases detected before a fraudulent transaction; (3) Step-Up Authentication Trigger Rate — proxy for detection sensitivity; (4) False Positive Rate — percentage of flags that resolve as legitimate activity; and (5) Detection-to-Response Latency — time from detection signal to containment action. Transaction fraud rate alone is an insufficient measure because it is blind to pre-monetization ATO activity.
Q: Why is cross-channel signal aggregation important for ATO detection?
A: Attackers frequently exploit channel-specific detection gaps by conducting reconnaissance on one channel — such as a mobile app — and executing monetization on another, such as the web or API. Siloed detection models that operate independently per channel cannot surface these cross-channel attack patterns. Aggregating risk signals across web, mobile, and API channels enables composite risk scoring that reflects the full attack surface, reducing the blind spots that sophisticated ATO campaigns actively probe. API endpoints are particularly undermonitored in most detection architectures despite being a primary surface for automated credential stuffing.
Q: How does digital impersonation connect to account takeover fraud?
A: Digital impersonation — phishing sites, clone sites, and spoofed login pages — is the primary mechanism through which credentials are harvested at Stage 1 of the ATO lifecycle. Detection architectures focused exclusively on login behavior miss this earliest signal layer entirely. Organizations with visibility into live phishing infrastructure targeting their brand can proactively flag at-risk accounts and trigger step-up authentication before a single login attempt occurs, compressing the fraud exposure window to near-zero for affected accounts. This upstream threat visibility represents the highest-leverage opportunity for detection-window compression in mature fraud operations.