Due to compromised accounts, financial institutions lose billions annually in unauthorized transactions and account-related fraud. Airlines suffer millions in fraudulent ticket purchases, and retailers face widespread loyalty fraud and resold gift cards. Automated, bot-driven takeovers further amplify the issue, driving costly credential-stuffing attacks that inflate operational costs and burn through budgets.
The list goes on, and the problem is only getting worse. Recent research shows that ATO attacks increased 250% in 2024, fueled by seasonal spikes and credential stuffing campaigns.
With ATO attacks’ increased complexity and diversity, businesses need dedicated account takeover solutions beyond reactive measures like fraud alerts for suspicious logins.
What are Account Takeover Solutions?
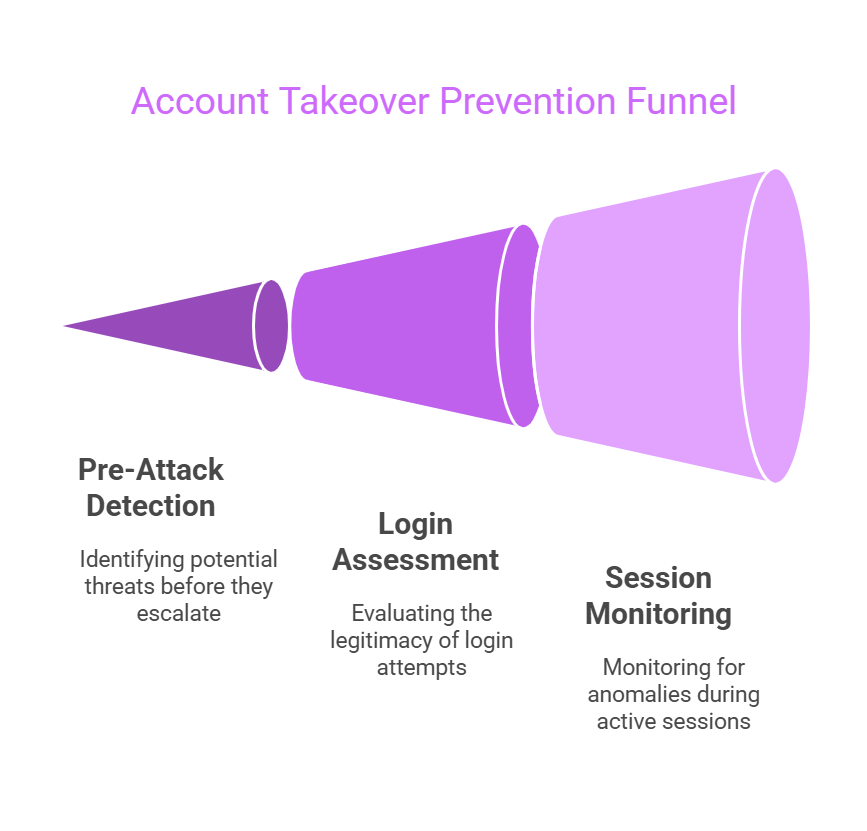
Account takeover (ATO) solutions are purpose-built anti-fraud tools for preventing, detecting, and mitigating unauthorized access to customers’ accounts. To assess whether an account session is legitimate, these platforms correlate multiple risk signals, such as device fingerprints, IP reputation, login velocity, and behavioral anomalies.
Some solutions focus on post-login defense. They monitor for session anomalies, unusual account behavior, and unauthorized device access. Others look at pre-attack reconnaissance (before the actual account is broken into) – think impersonating site setups, credential harvesting campaigns, credential stuffing attacks based on dark web lists of credentials, and so on. These preemptive solutions try to stop fraud before it impacts your customers.
Businesses need comprehensive ATO tools that complement each other. They should also incorporate these tools into broader fraud mitigation strategies.
Why You Need An Account Takeover Solution
1. Lowering Fraud Reimbursements
Account takeover fraud often leads to costly customer reimbursements. By proactively detecting and preventing ATO attacks, you significantly cut these payouts, directly reducing your fraud-related expenses. An effective ATO solution safeguards both your profit margins and customer satisfaction, ensuring fewer losses and stronger customer relationships.
2. Maintaining Regulatory Compliance
Account takeover incidents expose businesses not only to financial loss but also to regulatory scrutiny. Privacy and security standards like GDPR, CCPA, and PSD2 mandate robust protection of customer data and financial assets. An effective ATO solution ensures compliance, helping you avoid penalties, legal action, and damage to your brand’s reputation.
3. Lowering Customer Support Costs
ATO solutions lower customer support costs, first and foremost by decreasing the amount of incidents that need to be handled. Fewer compromised accounts reduce the need for manual account recovery and cut down on password resets and identity verification requests. Fewer incidents to handle also means reducing strain on customer service teams.
4. Reducing customer attrition
Beyond fraud prevention, ATO solutions also help preserve customer trust and engagement. When users experience an account takeover, many never return. A stolen balance, misused subscription, or hijacked travel rewards program often pushes customers to competitors. Strong account security prevents direct losses and builds confidence in digital services.
Key Features to Look For in Account Takeover Solutions
1. Real-Time Threat Detection
Many ATO defenses only react after an attack, but leading solutions identify threats in advance. Platforms like Memcyco can preempt ATO attempts by detecting spoofed websites in real-time. By alerting you as soon as your website is cloned, you can take action and prevent users from inserting their details on fake websites and risk having their accounts taken over.
The ability to stop an ATO attack before it even begins is valuable because attackers increasingly use automated tools, credential-stuffing botnets, and real-time phishing kits to access your customers’ accounts.
2. Device Fingerprinting
Once they break into an account, fraudsters use different techniques to blend in as legitimate users. Device fingerprinting features help distinguish between a real returning customer and an attacker using a fresh browser session or a residential proxy to mask their identity.
These solutions track browser characteristics, installed plugins, operating system details, and unique device signatures to detect inconsistencies. For example, suppose an account that usually logs in from a specific Windows machine suddenly appears from a headless browser running on AWS. In that case, an ATO solution will flag the session as high risk even if the credentials and IP address seem normal.
3. Credential Stuffing Prevention and Dark Web Monitoring
Most large-scale ATO attacks are bot-driven, and attackers use automated credential-stuffing tools to test thousands of username-password combinations per second. Look for ATO tools with credential stuffing prevention features, especially those that detect failed login attempts at the browser level, rather than waiting to analyze successful login attempts that reach your servers.
Some solutions automatically ingest dark web intelligence into risk assessment models. If an employee’s or customer’s credentials appear in a breach dump, the system can force a password reset before an attacker can exploit them. This proactive approach limits the window of opportunity for fraud.
Top 7 Account Takeover Solutions
1. Signifyd
Signifyd is designed for merchants battling large-scale fraud operations. It offers a global commerce network that analyzes billions of transactions across thousands of merchants to detect unusual account behavior. Fraudsters who steal credentials from one retailer and use them elsewhere can be flagged instantly because Signifyd has cross-merchant visibility into fraud rings, device farms, and repeat offenders.
Best for: Large e-commerce businesses that need real-time, network-wide fraud intelligence to stop repeat ATO offenders across multiple retailers.
“Simple to use, and takes the worry out of selling online.”
2. Memcyco
Memcyco offers a unique preemptive approach to ATO threats, helping to stop attackers before they even launch an account takeover. While traditional ATO defenses wait until fraudsters attempt login bypasses, Memcyco detects and disrupts pre-attack activities like phishing site setups, where fraudsters spin up copycat versions of your company’s site and lure customers to them.
Memcyco’s ATO protection extends to immediate protection if customers interact with impersonating sites. Red alerts and decoy data prevent them from submitting their real credentials to fraudsters. The platform is also agentless and cloud-based, which makes it easy to deploy across websites, customer portals, and mobile apps.
Best for: Banks, e-comm, and high-risk industries looking for innovative ATO prevention that stops attacks before they reach customers, rather than just detecting them mid-attack.
“What I love most about Memcyco is how it gives us pre-emptive foresight of ATOs in the making with real-time visibility into phishing attacks and impersonation scams before they hit our customers. Even if customers fall for scams, Memcyco dismantles card data and credentials theft attempts at the moment of impact.”
3. Telesign
Telesign focuses on identity-based ATO prevention, leveraging phone intelligence, behavioral biometrics, and real-time risk scoring to detect fraudulent access attempts. Telesign’s risk assessment engine analyzes login attempts, password resets, and session hijacking behaviors. It scores those events based on device reputation, network trust, and geo-location consistency. You can customize adaptive authentication workflows and enforce step-up security only when necessary.
Best for: Businesses that rely on phone-based authentication methods and need real-time SIM swap protection to prevent ATO fraud via MFA bypass.
“I like the API Integration that you can establish with this product as it allows you to connect it with tools you use…when engaging your customers.”
4. Beyond Identity
Instead of relying on credentials that can be stolen, phished, or brute-forced, Beyond Identity uses passwordless authentication with cryptographic key pairs stored in a user’s device TPM. Even if an attacker steals a username, there’s no password to compromise. The platform enforces continuous identity verification, meaning it doesn’t just authenticate users when they log in.
Best for: Companies looking to eliminate passwords and enforce device-bound authentication that’s very tough to get around.
“Beyond Identity has helped us reduce the time employees take to log in…Implementation was much easier than expected.”
5. Forter
Forter specializes in real-time decision-making for e-commerce ATO threats. It uses AI-powered risk scoring and behavioral analytics to block fraudulent logins before checkout fraud occurs. The platform detects device fingerprint mismatches and behavioral deviations. It then flags login attempts that don’t align with a user’s purchasing habits.
Best for: Retailers and online marketplaces that need real-time fraud prevention at both the login and transaction level.
“We are using this to prevent fraud in our airtime top-up business. Easy to implement, well API documentation, and good customer and technical support.”
6. Okta
Okta’s Adaptive Multi-Factor Authentication (AMFA) is built for enterprise-grade identity security, offering context-aware authentication policies to detect and block ATO attempts. Instead of using static authentication rules, Okta continuously assesses risk factors like IP reputation, geo-velocity, and device integrity before allowing access. If the tool suspects an ATO attempt, it can automatically enforce step-up verification, like biometric authentication or number-matching MFA challenges.
Best for: Apps or sites that need scalable, adaptive authentication and fraud-resistant login security to prevent consumer account takeovers without adding unnecessary friction.
“Easy Interface, dependable support team always ready to help if any questions regarding setting up automation and workflows.”
7. Imperva
Imperva’s Account Takeover Protection is designed for web application security and specializes in bot-driven ATO detection and credential stuffing prevention. It protects endpoints by analyzing high-volume login attempts, automation patterns, and dark web credential reuse in real-time. As part of its broader security stack, Imperva also provides a Web Application Firewall (WAF), which helps block malicious traffic and prevent automated attacks before they reach user accounts.
Best for: Businesses dealing with large-scale credential stuffing attacks that need bot mitigation and dark web monitoring for compromised credentials.
“(I like) the real-time review of account creation and login activities.”
Choosing the Right ATO Solution
Account takeover protection needs to be specialized and proactive, not just an afterthought where you try to stop suspicious logins. Therefore, a strong ATO toolset requires a combination of pre-attack intelligence, real-time action, and alternative authentication, such as passwordless or step-up.
Memcyco goes further than traditional fraud tools by detecting phishing sites impersonating your business and alerting you in real-time. This way, you can act quickly and minimize the damage caused by users entering their account details on the wrong site (where many ATO attacks stem from). If your users visit the fraudulent site, Memcyco provides Red Alerts to warn them and replaces their real data with decoy data to renter account credentials that are useless to attackers. Learn more here.